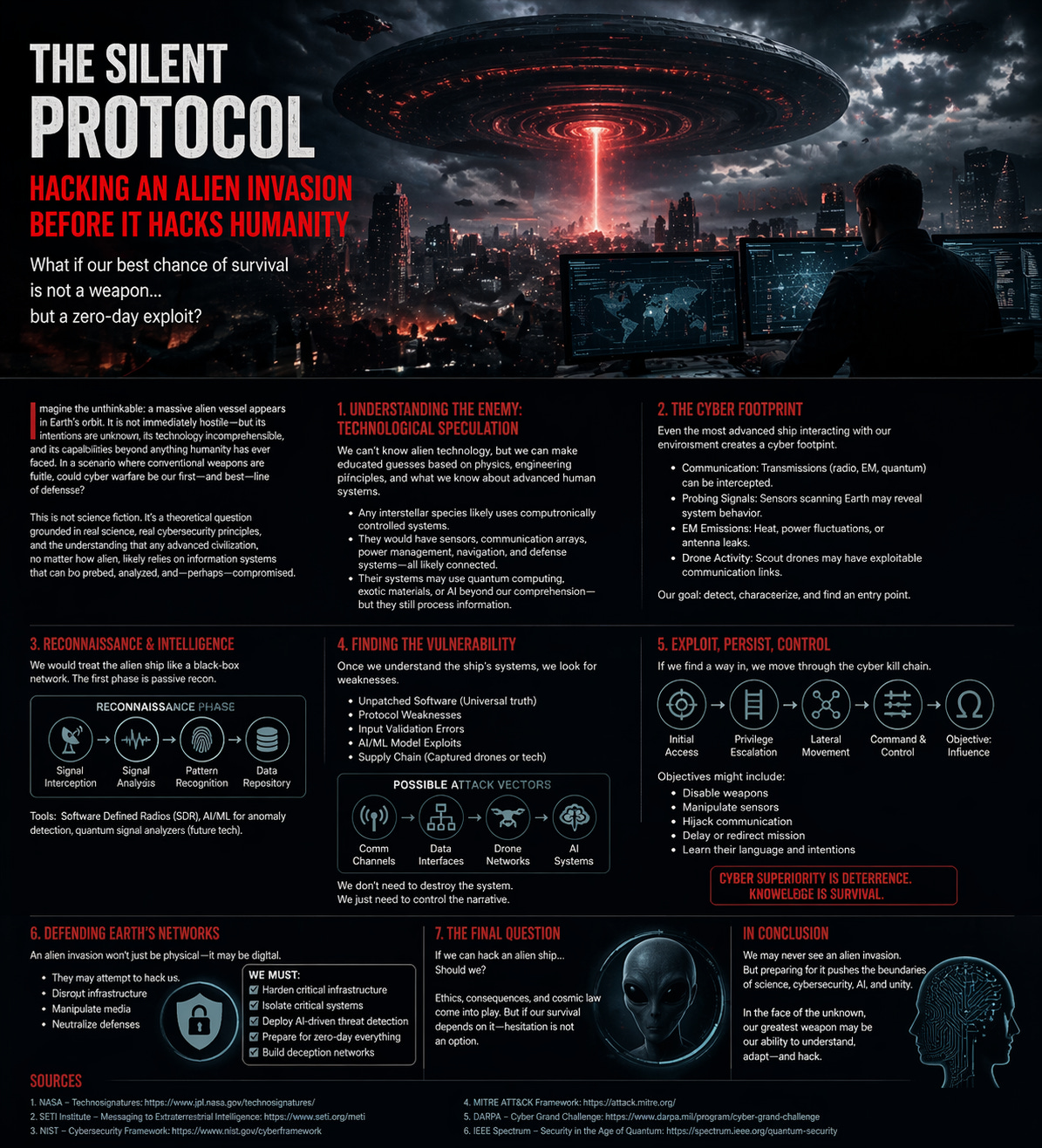
The Silent Protocol
Hacking an Alien Invasion Before It Hacks Humanity
What if our best chance of survival is not a weapon, but a zero-day exploit?
Imagine the unthinkable: a massive alien vessel appears in Earth’s orbit. It’s not immediately hostile—but its presence, technological capabilities, and intent are unknown. How would humanity respond to such an unprecedented crisis? Would our first—and best—line of defense be physical, or might the most effective means of survival involve something far less tangible?
This isn’t science fiction; it’s a theoretical scenario grounded in real resilience, advanced cybersecurity principles, and the understanding that any advanced civilization’s systems could be probed, analyzed, and—perhaps—compromised. But how would we begin? What if, instead of sending missiles or drones into space, humanity’s best hope for survival was a simple hack?
1. Understanding the Enemy: Technological Speculation
Before we discuss how to hack an alien invasion, we first need to consider the enemy’s technology. While we can’t fully understand what alien technology might look like, we can make educated guesses based on physics, engineering principles, and our knowledge of human systems. Even if the invading civilization is far more advanced, their systems would likely be built on principles we can recognize and exploit.
Most likely, the invaders would use complex computational technologies, including communication arrays, power management systems, and defense networks. They would likely have systems capable of interstellar communication, possibly quantum-based or leveraging radio, electromagnetic, or even more exotic methods. If we could detect their signals, probe their sensors, or find weak points in their systems, we could unlock vulnerabilities. It’s not a matter of if we can understand, but how.
2. The Cyber Footprint
One of the first rules of cybersecurity is that everything leaves a footprint. Alien ships and technology, no matter how advanced, would still interact with Earth’s environment, creating detectable signals. These signals would include:
Communication: Alien transmissions, whether radio, electromagnetic (EM), or quantum, could potentially be intercepted. Even if the encryption methods are beyond our comprehension, there may still be patterns, leaks, or weaknesses to exploit.
Probing Signals: Any sensors scanning Earth for signs of life or strategic assets would generate electromagnetic waves, heat patterns, or even fluctuations in Earth’s magnetic field. The mere presence of these probes could betray their position.
Drone Activity: Reconnaissance drones—both physical and cyber—might be sent to gather information about Earth’s defenses, possibly revealing exploitable weaknesses.
Our goal, therefore, would be to characterize and map these footprints, developing a deeper understanding of the alien ship’s internal architecture before launching a cyber attack.
3. Reconnaissance & Intelligence: The First Line of Defense
Before hacking into an alien system, we need a robust understanding of its vulnerabilities. This phase would start with reconnaissance, a passive form of intelligence gathering. Using Earth-based technologies like Software Defined Radios (SDR), we would detect anomalies in signal patterns, fluctuations in frequency, and any irregularities in atmospheric or EM signals.
Signal Interception: With SDR and advanced artificial intelligence (AI), we could intercept any stray communications or probe signals, learning about the ship’s communication protocols.
Pattern Recognition: AI-powered tools could help detect patterns in the transmission of data, indicating potential weaknesses in the alien encryption or network protocols.
Data Harvesting: A secondary objective could involve harvesting intercepted data for clues on software vulnerabilities, command structures, or military intent.
If we succeed at this stage, we could potentially gain valuable insights into the alien ship’s architecture and operational structure—key data that could make the difference when we launch our cyber countermeasures.
4. Finding the Vulnerability
Once we have a general understanding of the alien ship’s systems, we move on to the next step: finding exploitable vulnerabilities. Every system, no matter how advanced, has a weakness—whether that’s a software bug, faulty hardware, or a poorly executed security measure.
Unpatched Software: Even alien technology might rely on universal principles such as software to operate. Systems may be running unpatched code or have poorly configured security protocols.
Input Validation Errors: Just like human systems, alien technologies might suffer from simple input validation errors—mistakes where the system doesn’t properly authenticate or validate commands.
Protocol Weaknesses: There could be weaknesses in their communication protocols. The way they send and receive data may offer avenues for us to infiltrate.
Supply Chain Attacks: In the digital age, even our own supply chains are vulnerable. If alien invaders rely on sub-contracted resources or alien components, those systems might be easier to compromise.
At this point, we’d likely be looking for a way in—perhaps through captured drones, alien technology left on Earth, or an infiltrated communications channel.
5. Exploit, Persist, Control
Once a vulnerability is identified, the next step is to exploit it, persist within the system, and establish control. The goal here isn’t simply to disrupt the alien technology but to maintain influence over the ship, gathering intelligence and potentially disabling their weapon systems.
Privilege Escalation: The first step after identifying a weak point is privilege escalation. If we gain access to the system, we need to escalate our privileges to obtain full control, just as in conventional hacking.
Lateral Movement: From our initial access point, we would attempt to move laterally through the system. This could involve accessing communication channels, manipulating sensors, or even gaining access to the alien weapons systems.
Command & Control: Establishing a secure command and control channel would be necessary to maintain influence over the ship’s critical operations. Without this, our access would be fleeting.
In parallel, we would need to constantly monitor the system to ensure that our actions are not detected by the alien invaders, while also seeking to disrupt their communication systems to limit their ability to coordinate an effective counterattack.
6. Defending Earth’s Networks
While our offensive capabilities are critical, defense is just as important. An alien invasion wouldn’t just be physical—it could be digital. Their cyber warfare capabilities might target Earth’s critical infrastructure to create chaos before launching a full-scale attack. This phase would involve:
Hardening Critical Infrastructure: Strengthening Earth’s digital defenses would be vital to prevent the alien invaders from infiltrating our networks and systems.
Deploying Active Defenses: Developing active cyber defense mechanisms, such as AI-driven detection systems, would allow us to identify and counter alien attacks in real-time.
Preparing for Total Network Lockdown: In case of a large-scale breach, it may become necessary to isolate key infrastructure, such as communication networks, from the larger global internet to limit the spread of any malware.
7. The Final Question: Can We Win?
While hacking into an alien vessel may sound like the ultimate solution, there are ethical considerations. Would it be right to compromise an intelligent species’ technology? What if we don’t understand the full implications of our actions?
Moreover, how would we even ensure that the alien ship was truly compromised? Could the alien invaders retaliate? These are questions that, if an invasion were to happen, we would likely need to address on the fly.
One thing is certain: the more knowledge we gain about the alien invaders and their technology, the better our chances of survival. Cyber superiority would likely become the key to humanity’s defense—not just brute force, but intellectual and digital warfare.
In Conclusion
We may never see an alien invasion, but in case we do, humanity must be prepared—not just with weapons, but with the boundaries of science, cybersecurity, and unity. The fight for survival in the face of the unknown would require our greatest minds to understand, adapt, and hack back.
Cyber superiority is deterrence. Knowledge is survival.
Sources:
NASA – “Technologies for the Next Generation” - https://www.jpl.nasa.gov/technologies/
NIST – “Cybersecurity Framework” - https://www.nist.gov/cyberframework
DARPA – “Grand Challenge” - https://www.darpa.mil/program/grand-challenge
MITRE ATT&CK Framework -
https://attack.mitre.org/
DARPA – “Quantum Grand Challenge” - https://www.darpa.mil/program/quantum-grant-challenge
IEEE Spectrum – “Security in the Age of Quantum” - https://spectrum.ieee.org/quantum-computing